Introduction
Secure Access Service Edge platforms combine networking and security into a single cloud-delivered approach to protect users, devices, and branch locations as they access the internet, SaaS apps, and private applications. In simple terms, SASE brings functions like secure web gateway, zero trust network access, cloud access security broker, firewall controls, and traffic optimization together under one policy and one management plane. Instead of backhauling traffic through a data center, users connect to nearby cloud security edges that enforce identity-based access rules, inspect web traffic, prevent data leaks, and provide consistent protection anywhere.
SASE matters because work is no longer tied to office networks. Remote users, distributed branches, contractors, and cloud apps are now normal. Traditional VPN plus separate web security tools often create gaps, inconsistent policies, and operational overhead. SASE helps unify these controls, reduce complexity, improve visibility, and support a consistent security posture across all locations. It also helps reduce risk from phishing, malware, cloud app misconfigurations, and uncontrolled data sharing, while maintaining good performance for real business apps.
Common use cases include:
- Replacing VPN and centralized internet backhaul for remote users and branches
- Enforcing consistent web and SaaS access policies across locations
- Protecting users from phishing, malware, and risky web destinations
- Controlling sensitive data movement in cloud apps and web uploads
- Simplifying security operations through unified logs, policies, and workflows
What buyers should evaluate:
- Breadth of capabilities: SWG, ZTNA, CASB, firewall controls, data protection
- Identity-driven policy depth and device posture support
- Performance and reliability across global users and branch sites
- Encrypted traffic inspection quality and privacy controls
- SaaS app coverage, shadow IT visibility, and data governance strength
- Policy management usability and role-based administration
- Logging, reporting, and investigation workflows for security teams
- Integration with identity providers, endpoint security, and security operations tools
- Migration approach from legacy VPN, proxies, and branch firewalls
- Licensing simplicity and how features are packaged for growth
Best for: Security and network teams modernizing remote access and branch security with a unified cloud security approach.
Not ideal for: Very small teams with simple needs and minimal remote access, where basic endpoint security plus straightforward identity controls may be enough.
Key Trends in SASE Platforms
- Consolidation of web security, ZTNA, and SaaS governance into one platform
- Stronger identity and device posture signals driving policy decisions
- More focus on data protection for uploads, downloads, and SaaS sharing
- Increased use of global edge networks to improve performance and reduce latency
- Simplified branch connectivity models with cloud-managed policies
- More automation for rollout, policy tuning, and incident response workflows
- Better visibility into shadow IT, risky integrations, and SaaS misconfigurations
- More flexible SSL inspection controls to balance privacy and security needs
- Growth of unified dashboards for security posture and business risk outcomes
- Continued shift away from legacy VPN and on-prem proxy architectures
How We Selected These Tools
- Strong adoption and credibility for cloud-delivered security and networking
- Real-world coverage for core SASE building blocks: SWG, ZTNA, CASB alignment
- Operational usability including centralized policy management and reporting
- Performance and reliability expectations for global and remote user coverage
- Integration readiness with identity, endpoint, and security operations ecosystems
- Scalability across large distributed workforces and branch environments
- Strength of data protection and cloud app governance capabilities
- Flexibility across deployment models including agents, tunnels, and branch setups
- Support maturity and documentation quality for rollout success
- Balanced mix of market leaders and cloud-first platforms
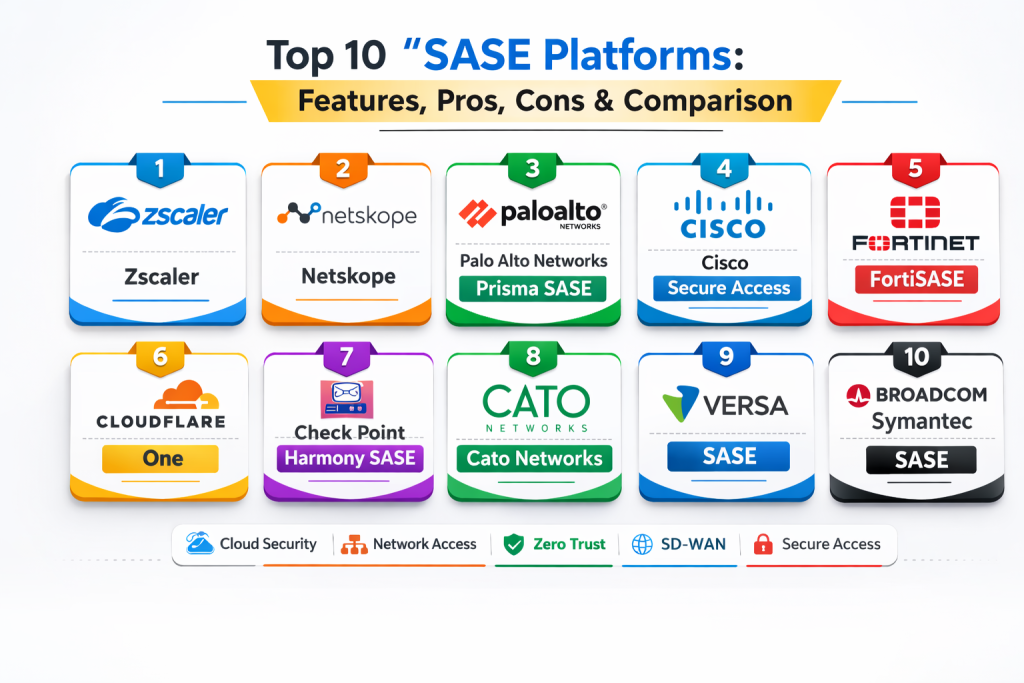
Top 10 SASE Platforms
1) Zscaler
Zscaler is widely used for cloud-delivered security with strong web protection and private access capabilities. It fits organizations that want a mature, scalable platform for distributed users and global policy enforcement.
Key Features
- Cloud secure web gateway with strong filtering and threat prevention
- Private application access with app-level segmentation options
- Identity-driven policies with user and group enforcement
- Encrypted traffic inspection with flexible policy controls
- Data protection options for web and cloud usage patterns
- Visibility dashboards for threats, policy outcomes, and investigations
Pros
- Strong scalability for large distributed organizations
- Mature policy model and reporting capabilities
Cons
- Policy tuning and rollout planning are important for smooth adoption
- Complex environments may require experienced administration
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Varies / Not publicly stated
Integrations & Ecosystem
Designed to fit identity-driven and operations-driven security stacks.
- Identity provider integrations for user-based policies
- SIEM exports for investigations and correlation
- APIs for automation and reporting workflows
- Device posture integrations depending on environment
Support & Community
Enterprise support is common; documentation is strong; community footprint is broad.
2) Netskope
Netskope is known for combining web security with strong visibility and control of SaaS apps. It fits SaaS-heavy organizations that want data protection and cloud app governance as part of their secure access model.
Key Features
- Secure web gateway controls with category and risk-based policies
- Cloud app visibility and governance controls for SaaS usage
- Data protection policies for uploads, downloads, and sharing workflows
- Identity and device context policies for access decisions
- Reporting dashboards for cloud usage, risk, and investigations
- Integration readiness for security operations workflows
Pros
- Strong SaaS visibility and data protection focus
- Useful for cloud-first environments and remote work models
Cons
- Policy tuning is required to keep workflows low-friction
- Connector coverage should be validated for your SaaS portfolio
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Varies / Not publicly stated
Integrations & Ecosystem
Built to connect cloud policies into operational workflows.
- Identity provider integration for user-based enforcement
- SIEM exports for analytics and investigations
- APIs for automation and reporting
- Ticketing integration patterns for incident workflows
Support & Community
Enterprise support options are common; documentation is solid; community footprint is broad.
3) Palo Alto Networks Prisma SASE
Palo Alto Networks Prisma SASE combines secure access, threat prevention, and policy governance in a cloud-delivered model. It fits organizations seeking unified control aligned with broader security operations programs.
Key Features
- Secure web gateway and threat prevention capabilities
- Private access controls for internal apps with segmentation options
- Policy management for users, branches, and distributed environments
- Visibility dashboards for threats and access outcomes
- Integration readiness for security operations workflows
- Scalable model for multi-region users and branch connectivity
Pros
- Strong enterprise fit with broad security coverage
- Useful for standardizing policy across different environments
Cons
- Setup and tuning can be complex at large scale
- Feature breadth can feel heavy if scope is not clearly defined
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Varies / Not publicly stated
Integrations & Ecosystem
Designed for enterprise security operations alignment.
- Identity provider integration for user-aware policies
- SIEM exports for correlation and investigations
- APIs for automation and reporting
- Ticketing integration patterns for operational workflows
Support & Community
Enterprise support is common; documentation is strong; community footprint is broad.
4) Cisco Secure Access
Cisco Secure Access provides a secure access model aligned with networking and security operations workflows. It fits organizations that want strong integration into existing Cisco security and network ecosystems.
Key Features
- Secure web access controls for internet and SaaS usage
- Private app access capabilities aligned with identity policies
- Policy management for users and distributed environments
- Visibility dashboards for monitoring, investigations, and audits
- Integration readiness for security operations workflows
- Support for branch and remote user connectivity patterns
Pros
- Strong ecosystem fit for Cisco-aligned organizations
- Practical integration into security operations workflows
Cons
- Configuration and tuning may require expertise
- Feature depth depends on environment scope and rollout design
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Designed for operational integration with broader network security workflows.
- Identity provider integration for access control policies
- SIEM exports for investigations and reporting
- APIs for automation and operational workflows
- Ticketing integration patterns for incident and request workflows
Support & Community
Enterprise support options are common; documentation is established; community footprint is broad.
5) Fortinet FortiSASE
Fortinet FortiSASE offers cloud-delivered security capabilities aligned with Fortinet security stacks. It fits organizations that want unified secure access and consistent policies across users and branches.
Key Features
- Secure web gateway controls and policy enforcement
- Private access capabilities aligned with identity-driven rules
- Visibility dashboards for security monitoring and governance
- Integration options with device posture and endpoint signals
- Scalable model for remote users and branch connectivity
- Reporting for investigations and compliance tracking
Pros
- Strong fit for organizations standardizing on Fortinet tooling
- Practical approach to unifying access and security controls
Cons
- Policy tuning needed to reduce user friction and alert noise
- Architecture planning required for complex multi-region environments
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Designed to align with identity and operational security workflows.
- Identity provider integration for user-based policies
- SIEM exports for investigations and dashboards
- APIs for automation and reporting
- Endpoint posture integrations depending on setup
Support & Community
Enterprise support options are common; documentation is solid; community footprint is broad.
6) Cloudflare One
Cloudflare One combines edge-based security controls and connectivity features with a focus on performance. It fits organizations that want fast secure access for globally distributed users and branches.
Key Features
- Secure web filtering and threat blocking at the edge
- Private application access with identity-based policies
- Support for browser-based access and client-based connectivity
- Visibility dashboards for traffic, threats, and policy outcomes
- Global edge routing designed to reduce latency
- Integration options for identity and device context policies
Pros
- Strong performance profile for global users
- Practical rollout options with modern edge connectivity patterns
Cons
- Some advanced enterprise policy needs require careful design
- Depth depends on configuration choices and enforcement scope
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Designed to connect identity-based policies into operations workflows.
- Identity provider integrations for access control
- APIs for automation and reporting
- Exports for monitoring and analytics pipelines
- Device posture integrations depending on environment
Support & Community
Support options vary by plan; documentation is strong; community footprint is broad.
7) Check Point Harmony SASE
Check Point Harmony SASE offers secure access capabilities aligned with Check Point security governance models. It fits organizations that want policy-driven controls and access governance with structured monitoring.
Key Features
- Web access controls with threat prevention workflows
- Private access capabilities aligned with identity-based policies
- Policy management for distributed users and remote access needs
- Visibility dashboards for access monitoring and investigations
- Integration readiness for security operations workflows
- Reporting support for audits and governance tracking
Pros
- Useful fit for organizations aligning access with governance models
- Practical policy enforcement for private app access
Cons
- Feature depth depends on environment scope and deployment design
- Tuning required to balance control and user experience
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Designed to connect access controls into operational workflows.
- Identity provider integration for user policies
- SIEM exports for investigations and reporting
- APIs for automation and operational workflows
- Ticketing integration patterns for access request processes
Support & Community
Support options vary; documentation is solid; community footprint is moderate.
8) Cato Networks
Cato Networks delivers a cloud-native secure access model with integrated networking and security capabilities. It fits organizations that want a unified approach for branch connectivity and remote user protection.
Key Features
- Cloud-delivered security controls for internet and SaaS access
- Private access capabilities for internal applications
- Integrated connectivity for branches and distributed locations
- Policy management and dashboards for monitoring and governance
- Visibility into traffic patterns and security events
- Scalable deployment model for multi-site environments
Pros
- Strong unified approach for branch connectivity and security
- Practical model for organizations modernizing distributed networks
Cons
- Feature depth should be validated for advanced data protection needs
- Migration planning needed when replacing multiple legacy tools
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Designed to integrate into enterprise identity and monitoring workflows.
- Identity provider integration for user and group policies
- SIEM exports for investigations and correlation
- APIs for automation and reporting
- Ticketing integration patterns for operational workflows
Support & Community
Enterprise support options are common; documentation is solid; community footprint is broad.
9) Versa SASE
Versa SASE provides secure access capabilities often used for enterprise and service provider environments. It fits teams that want flexible deployment models and strong policy controls for distributed access.
Key Features
- Web security controls and policy enforcement
- Private access capabilities aligned with identity-driven policies
- Flexible deployment support for distributed users and branches
- Visibility dashboards for traffic, threats, and governance tracking
- Integration readiness for security operations workflows
- Scalable model for multi-site and multi-tenant environments
Pros
- Flexible deployment model for complex distributed environments
- Strong policy control options for segmentation and governance
Cons
- Administration complexity can be higher depending on architecture
- Requires planning to align policies with real-world workflows
Platforms / Deployment
Web, Windows, macOS, iOS, Android
Cloud, Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Designed to integrate with identity and security operations tooling.
- Identity provider integration for user-based policies
- SIEM exports for analysis and investigations
- APIs for automation and reporting
- Ticketing integration patterns for operational workflows
Support & Community
Support options vary; documentation is established; community footprint is moderate.
10) Broadcom Symantec SASE
Broadcom Symantec SASE aligns mature web security controls with cloud-delivered access governance patterns. It fits organizations that want structured policies and enterprise governance reporting.
Key Features
- Secure web gateway controls with mature policy governance
- Encrypted traffic inspection with flexible policy enforcement
- Reporting dashboards for investigations and compliance tracking
- Identity-driven policy enforcement for user-based controls
- Support for distributed users and branch environments
- Integration readiness for security operations workflows
Pros
- Mature governance model for enterprise web security programs
- Useful reporting for audits and structured compliance needs
Cons
- Administration can be complex and requires tuning
- Feature packaging should be validated for your target capabilities
Platforms / Deployment
Web, Windows, macOS
Cloud, Hybrid
Security & Compliance
Varies / Not publicly stated
Integrations & Ecosystem
Designed for enterprise governance and operational integration.
- SIEM exports for investigations and reporting
- APIs for automation and reporting workflows
- Identity provider integration for user-aware policies
- Ticketing integration patterns for incident and request handling
Support & Community
Enterprise support options are common; documentation is established; community footprint is broad.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Zscaler | Mature cloud security at global scale | Web, Windows, macOS, iOS, Android | Cloud | Strong scalability and policy maturity | N/A |
| Netskope | SaaS-heavy environments needing strong data protection | Web, Windows, macOS, iOS, Android | Cloud | Cloud app visibility plus data controls | N/A |
| Palo Alto Networks Prisma SASE | Unified enterprise security policy and threat prevention | Web, Windows, macOS, iOS, Android | Cloud | Broad security coverage for enterprises | N/A |
| Cisco Secure Access | Cisco-aligned secure access and operational integration | Web, Windows, macOS, iOS, Android | Cloud | Strong ecosystem alignment | N/A |
| Fortinet FortiSASE | Fortinet-aligned unified access and security controls | Web, Windows, macOS, iOS, Android | Cloud | Practical unified security approach | N/A |
| Cloudflare One | Edge-based security with strong global performance | Web, Windows, macOS, iOS, Android | Cloud | Global edge routing performance | N/A |
| Check Point Harmony SASE | Policy-driven governance aligned with security programs | Web, Windows, macOS, iOS, Android | Cloud | Governance-friendly access policies | N/A |
| Cato Networks | Unified branch connectivity and cloud-native security | Web, Windows, macOS, iOS, Android | Cloud | Integrated networking plus security | N/A |
| Versa SASE | Flexible distributed access with strong policy controls | Web, Windows, macOS, iOS, Android | Cloud, Hybrid | Flexible deployment for complex networks | N/A |
| Broadcom Symantec SASE | Mature governance-focused web security and reporting | Web, Windows, macOS | Cloud, Hybrid | Enterprise policy and reporting maturity | N/A |
Evaluation and Scoring of SASE Platforms
Weights used: Core features (25%), Ease of use (15%), Integrations and ecosystem (15%), Security and compliance (10%), Performance and reliability (10%), Support and community (10%), Price and value (15%).
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Zscaler | 9 | 7 | 8 | 8 | 9 | 8 | 6 | 7.85 |
| Netskope | 9 | 7 | 8 | 8 | 8 | 7 | 6 | 7.65 |
| Palo Alto Networks Prisma SASE | 9 | 6 | 8 | 8 | 8 | 8 | 6 | 7.55 |
| Cisco Secure Access | 8 | 7 | 8 | 7 | 8 | 7 | 6 | 7.25 |
| Fortinet FortiSASE | 8 | 7 | 7 | 7 | 8 | 7 | 7 | 7.45 |
| Cloudflare One | 8 | 8 | 7 | 7 | 9 | 7 | 8 | 7.95 |
| Check Point Harmony SASE | 7 | 7 | 6 | 7 | 7 | 6 | 7 | 6.85 |
| Cato Networks | 8 | 8 | 7 | 7 | 8 | 7 | 7 | 7.60 |
| Versa SASE | 8 | 6 | 7 | 7 | 8 | 6 | 6 | 6.95 |
| Broadcom Symantec SASE | 8 | 6 | 7 | 7 | 7 | 7 | 6 | 6.95 |
How to interpret the scores:
- Scores are comparative within this list and help shortlist based on your security and networking consolidation goals.
- Core reflects coverage for web security, private access, cloud app governance alignment, and policy enforcement depth.
- Ease reflects rollout effort, day-to-day admin workload, and policy tuning complexity.
- A pilot should validate latency, inspection coverage, SaaS policy needs, and migration effort from existing tools.
Which SASE Platform Is Right for You?
Solo / Freelancer
Full SASE platforms are usually more than you need unless you manage multiple client environments. If you do, prioritize simple rollout, fast performance, and clear identity-based policies.
SMB
SMBs should prioritize ease of deployment, strong web protection, and straightforward remote access replacement. A platform with simple policy templates and low admin overhead is often the best fit.
Mid-Market
Mid-market teams should look for stronger data protection, better SaaS visibility, and operational integrations for logging and response workflows. Choose a platform that scales policy across departments without becoming hard to manage.
Enterprise
Enterprises should prioritize policy governance, segmentation depth, global performance, and evidence-rich reporting. Validate how the platform supports multiple business units, contractor access, and complex app portfolios.
Budget vs Premium
Budget options can provide good baseline SWG and ZTNA controls, but premium platforms often reduce workload through better automation, stronger data protection, and broader connectors. Choose based on risk exposure and team capacity.
Feature Depth vs Ease of Use
If you have strong security engineering capacity, deeper policy controls can provide better long-term security outcomes. If your team is small, prioritize usability, high-signal alerts, and simple operational workflows.
Integrations and Scalability
Confirm identity provider integration, device posture support, SIEM export, and ticketing workflows. Scalability means onboarding new users, branches, and apps without redesigning routing or rewriting policies constantly.
Security and Compliance Needs
If compliance matters, focus on audit-friendly logs, policy traceability, evidence trails for enforcement actions, and consistent controls across all user locations. Also confirm that encrypted traffic inspection can be managed with privacy-aware policies.
Frequently Asked Questions
1) What is SASE in simple terms?
It is a cloud-delivered approach that combines networking and security so users can safely access the internet, SaaS, and private apps from anywhere.
2) How is SASE different from using separate tools?
Separate tools often create policy gaps and higher operational overhead. SASE aims to unify policy, visibility, and enforcement under one platform.
3) Does SASE replace VPN?
In many cases yes, especially through ZTNA capabilities that connect users to specific apps rather than broad network access.
4) Does SASE include secure web gateway protection?
Most SASE platforms include SWG features such as web filtering, threat prevention, and encrypted traffic inspection.
5) Can SASE help stop data leaks in SaaS apps?
Many platforms provide CASB-style controls and data protection policies to limit risky uploads, downloads, and sharing behaviors.
6) What is the biggest challenge in adopting SASE?
Migration planning. Replacing VPN, on-prem proxies, and branch firewalls requires staged rollout, careful routing design, and policy tuning.
7) Will SASE slow down user performance?
A well-designed SASE rollout can improve performance by using nearby cloud edges instead of backhauling traffic. A pilot should confirm latency and app experience.
8) How do we reduce false positives and user disruption?
Start with monitor mode, apply high-risk policies first, create a structured exception process, and expand gradually after tuning.
9) How do we measure SASE success?
Track reduced VPN use, fewer web-based incidents, improved visibility into cloud usage, lower policy violations, and simpler operational workflows.
10) How do we choose the right SASE platform?
Shortlist two or three platforms, run a pilot, validate performance and enforcement, confirm SaaS and private app coverage, and check operational reporting quality.
Conclusion
SASE platforms help organizations modernize security and connectivity by delivering web protection, private application access, and cloud governance through a unified cloud approach. The best platform depends on your workforce distribution, branch footprint, SaaS dependency, and how much policy depth and data protection you need. Start by shortlisting two or three SASE options that match your current tools and your target architecture, then run a pilot with a small user group and a limited set of policies. Measure latency, false positives, ease of troubleshooting, and how well the platform supports your critical SaaS apps and private applications. After tuning, expand gradually with clear governance for exceptions and policy changes. Over time, strong SASE adoption should reduce VPN reliance, simplify security operations, and deliver measurable risk reduction without harming productivity.
Best Cardiac Hospitals Near You
Discover top heart hospitals, cardiology centers & cardiac care services by city.
Advanced Heart Care • Trusted Hospitals • Expert Teams
View Best Hospitals