Introduction
Artifact and container signing is a critical security practice used to verify the origin and integrity of software components. In a modern software supply chain, a “signed” artifact is cryptographically linked to a specific identity or build process, ensuring that the code you deploy is exactly what was produced in your trusted environment. This process prevents “man-in-the-middle” attacks where malicious actors might swap a legitimate container image for a compromised one.
In the current landscape, the Sigstore project has revolutionized this space by introducing keyless signing. Instead of managing complex, long-lived private keys that are prone to theft or loss, developers can now use short-lived certificates tied to their existing identities (such as GitHub or Google). This shift towards identity-based security makes it significantly easier for organizations to adopt Zero Trust principles across their delivery pipelines.
Real-World Use Cases
- CI/CD Security: Automatically signing container images immediately after a successful build to ensure only authorized code reaches the registry.
- Compliance & Auditing: Providing a tamper-proof transparency log of every software release for regulatory requirements like SOC 2 or SLSA.
- Kubernetes Admission Control: Blocking any container from running in a production cluster if it lacks a valid, verified signature.
- Open Source Distribution: Allowing users to cryptographically verify that a downloaded package or binary was actually released by the official maintainers.
- SBOM Integrity: Signing Software Bill of Materials (SBOMs) to guarantee that the list of dependencies provided with a release has not been altered.
Evaluation Criteria for Buyers
- Keyless Support: Does the tool support identity-based signing to eliminate the burden of key management?
- Registry Compatibility: How well does it integrate with standard OCI registries (Docker Hub, ACR, ECR, GCR)?
- Enforcement Capabilities: Can it actively block unsigned artifacts at the deployment level?
- Transparency Logging: Does it provide a public or private audit trail of all signing events?
- Automation Friendliness: How easily can the tool be embedded into existing GitHub Actions, GitLab, or Jenkins pipelines?
- Policy Flexibility: Can you define complex rules, such as requiring multiple signatures for a single artifact?
- Ease of Use: Is the CLI intuitive for developers, or does it require deep cryptographic expertise?
Best for: DevSecOps engineers, security architects, and platform teams building cloud-native applications who need to secure their software supply chain.
Not ideal for: Teams working entirely in legacy non-containerized environments or those with no requirement for verifiable software provenance.
Key Trends in Artifact/Container Signing
- The Decline of Legacy Standards: Older systems like Docker Content Trust (Notary v1) are being retired in favor of Sigstore and the OCI-native Notary Project.
- Widespread OIDC Adoption: Identity-based signing via OpenID Connect is becoming the default standard for cloud-native pipelines.
- Ephemeral Certificate Authority: The use of short-lived certificates that expire in minutes is drastically reducing the risk of key compromise.
- Integration with SBOMs: Signing is no longer just for images; it is now regularly applied to security metadata and vulnerability scan reports.
- Public Transparency Logs: Global audit logs like Rekor are becoming the “source of truth” for verifying the history of software releases.
- Kubernetes-Native Enforcement: Security is moving from manual checks to automated admission controllers that govern cluster health in real-time.
- Hardware Security Integration: For high-security environments, tools are increasingly supporting hardware keys and KMS-backed signing identities.
- SLSA Framework Alignment: Tools are being redesigned to help organizations reach higher levels of the Supply Chain Levels for Software Artifacts (SLSA) framework.
How We Selected These Tools
The tools on this list represent the current state-of-the-art in software supply chain security. Our methodology focused on projects that have strong community backing, particularly those within the Linux Foundation and CNCF ecosystems. We prioritized tools that support the modern “keyless” workflow, as this is where the industry is moving. We also ensured a balance between signing tools (creation) and verification tools (enforcement), as both are required for a complete security posture. Finally, we looked for high levels of interoperability with standard container registries and Kubernetes environments.
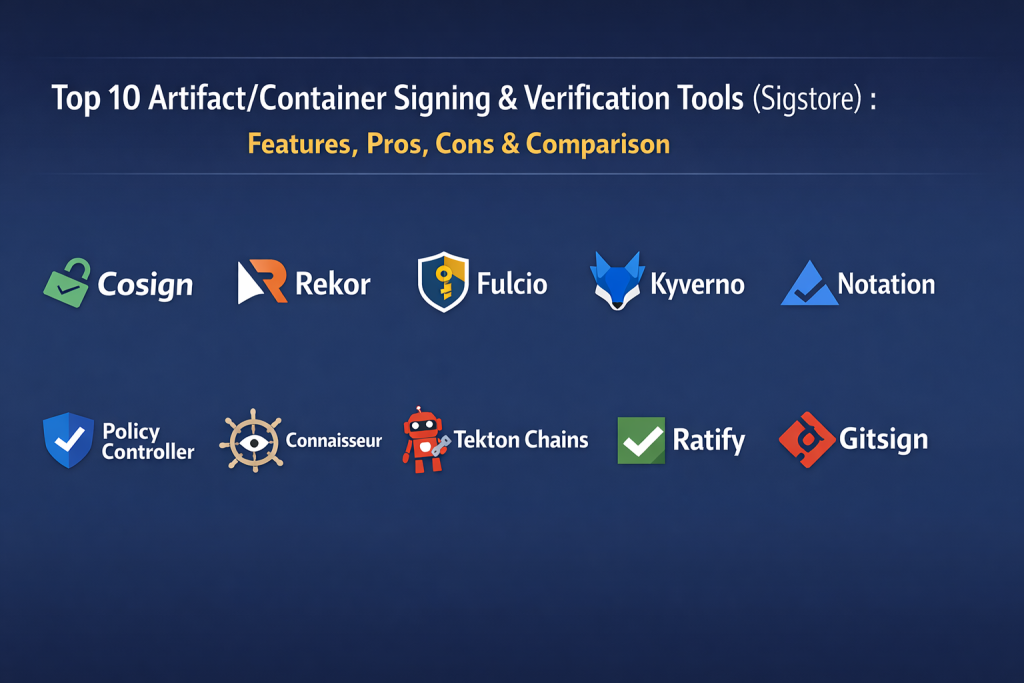
Top 10 Artifact/Container Signing & Verification Tools
1. Sigstore Cosign
Cosign is the flagship tool of the Sigstore project. It is a lightweight CLI designed to sign and verify OCI artifacts, such as container images, directly in a registry. It pioneered the concept of keyless signing, allowing users to sign artifacts using an OIDC identity without managing permanent cryptographic keys.
Key Features
- Keyless Signing: Uses OIDC identities from providers like GitHub or Google to generate ephemeral certificates.
- OCI-Native Storage: Signatures and attestations are stored directly in the registry alongside the image.
- Attestation Support: Can sign and attach metadata like SBOMs and vulnerability reports.
- KMS Integration: Supports cloud-based key management services (AWS, GCP, Azure) for traditional key-based signing.
- Recursive Signing: Ability to sign multiple tags or digests within a single command.
Pros
- Simple, developer-friendly command-line interface.
- Extremely fast adoption and massive community support.
Cons
- Requires a running transparency log (like Rekor) for the full keyless benefit.
- Managing public keys for verification in air-gapped environments can be complex.
Platforms / Deployment
Windows / macOS / Linux — Cloud / Hybrid
Security & Compliance
Uses short-lived certificates and public transparency logs for auditability.
Integrations & Ecosystem
Integrates with all major OCI registries and CI/CD platforms. It is the core tool used by GitHub for its “Artifact Attestations” feature.
Support & Community
One of the fastest-growing projects in the OpenSSF and Linux Foundation, with extensive documentation and professional training.
2. Sigstore Rekor
Rekor is the transparency log component of the Sigstore ecosystem. It provides an immutable, append-only ledger that records all signing events. This allows anyone to verify that a signature was created at a specific time and by a specific identity, even after the signing certificate has expired.
Key Features
- Immutable Ledger: Records signatures, certificates, and hashed artifacts in a tamper-proof log.
- Searchable API: Allows users to query the log by image digest, email identity, or public key.
- Artifact Transparency: Provides a public record that prevents “split-view” attacks.
- Integrated Timestamping: Acts as a trusted time-stamping authority for signatures.
- High Scalability: Designed to handle millions of entries for global open-source ecosystems.
Pros
- Provides undeniable proof of when and by whom an artifact was signed.
- Eliminates the need for long-lived certificate revocation lists (CRLs).
Cons
- Public logs may expose metadata that sensitive organizations wish to keep private.
- Deploying a private instance of Rekor is technically demanding.
Platforms / Deployment
Linux — Cloud / Self-hosted
Security & Compliance
Provides a robust audit trail required for many high-security compliance frameworks.
Integrations & Ecosystem
Works seamlessly with Cosign, Fulcio, and other Sigstore components to provide a complete trust root.
Support & Community
Strong community support from the Sigstore project and major cloud providers.
3. Sigstore Fulcio
Fulcio is a free certificate authority (CA) that issues short-lived certificates based on an OpenID Connect (OIDC) identity. It is the engine that makes “keyless” signing possible by verifying that a user owns an email address or a workload identity before granting a temporary signing certificate.
Key Features
- OIDC Identity Verification: Bridges the gap between web identities and cryptographic keys.
- Ephemeral Certificates: Issues certificates that are only valid for a few minutes.
- Automated Issuance: Designed for machine-to-machine communication in CI/CD pipelines.
- Root of Trust: Provides a centralized, trusted authority for identity-based signing.
- Workload Identity Support: Can issue certificates to GitHub Runners, GitLab Jobs, and Kubernetes pods.
Pros
- Removes the risk of stolen private keys being used for malicious signing.
- Simplifies the developer experience by removing manual key generation.
Cons
- Creates a centralized dependency on the Fulcio service.
- Requires a stable internet connection to communicate with the CA.
Platforms / Deployment
Linux — Cloud / Self-hosted
Security & Compliance
Greatly enhances security by moving away from long-lived secrets.
Integrations & Ecosystem
Fully integrated into the Sigstore workflow and supported by major identity providers.
Support & Community
Directly supported by the Sigstore project and OpenSSF.
4. Kyverno
Kyverno is a Kubernetes-native policy engine that can enforce image verification at the cluster level. It uses a “verifyImages” rule to check signatures created by Cosign, ensuring that only trusted containers are allowed to start in a namespace.
Key Features
- Declarative Policies: Define security rules using standard Kubernetes YAML.
- Signature Verification: Natively supports verifying Cosign signatures and attestations.
- Keyless & Key-Based: Can verify signatures using public keys or OIDC identities.
- Attestation Filtering: Can block images that don’t have a specific SBOM or scan report attached.
- Audit and Enforce Modes: Allows teams to test policies before actively blocking traffic.
Pros
- Extremely easy for Kubernetes administrators to manage without learning new languages.
- Provides detailed reports on policy violations directly in the cluster.
Cons
- Primarily focused on Kubernetes; not applicable to other deployment types.
- Large policy sets can impact the performance of the API server.
Platforms / Deployment
Kubernetes — Cloud / Hybrid
Security & Compliance
Essential for implementing the “Enforce” stage of a secure supply chain.
Integrations & Ecosystem
Deeply integrated with the Kubernetes ecosystem and the Sigstore project.
Support & Community
A CNCF graduated project with a very large and helpful community.
5. Notary Project (Notation)
Notation is a CLI tool from the Notary Project (v2) that focuses on signing and verifying OCI artifacts. It is the primary alternative to Sigstore and is heavily supported by major cloud providers like Microsoft and Amazon for their respective registries.
Key Features
- OCI Standard Compliance: Built specifically to follow the latest OCI specifications for signatures.
- Plugin-Based Architecture: Supports plugins for various KMS and secret stores.
- X.509 Certificate Support: Uses standard certificate formats familiar to enterprise IT teams.
- Cross-Registry Support: Designed to work across different registry implementations without issues.
- Trust Store Management: Provides clear commands for managing trusted root certificates.
Pros
- Excellent integration with Azure Key Vault and AWS KMS.
- Follows traditional enterprise PKI models that many security teams already understand.
Cons
- Lacks the widespread “keyless” public infrastructure that Sigstore offers.
- Smaller community adoption compared to the Sigstore ecosystem.
Platforms / Deployment
Windows / macOS / Linux — Cloud / Hybrid
Security & Compliance
Strongly aligned with traditional enterprise security standards.
Integrations & Ecosystem
Primary tool for Azure Container Registry (ACR) and AWS Elastic Container Registry (ECR).
Support & Community
A CNCF sandbox project with strong backing from major cloud vendors.
6. Sigstore Policy Controller
This is the official Kubernetes admission controller for the Sigstore project. It is specifically designed to enforce the policies surrounding Cosign signatures, attestations, and transparency log entries within a cluster.
Key Features
- Admission Webhook: Intercepts pod creation requests to verify container images.
- Rekor Integration: Can verify that a signature exists in the transparency log before allowing a deployment.
- Complex Policy Logic: Supports multi-signature requirements and specific identity checks.
- Cluster-Wide Enforcement: Can be applied across the entire cluster or specific namespaces.
- Lightweight Design: Focused solely on verification, making it very efficient.
Pros
- The “official” way to verify Sigstore signatures in Kubernetes.
- Tight integration with the Rekor transparency log for maximum security.
Cons
- More specialized and less flexible than general-purpose engines like Kyverno.
- Requires knowledge of the Sigstore ecosystem to configure effectively.
Platforms / Deployment
Kubernetes — Cloud / Hybrid
Security & Compliance
Provides the highest level of assurance for Sigstore-based workflows.
Integrations & Ecosystem
Part of the core Sigstore project.
Support & Community
Growing community of security-conscious Kubernetes users.
7. Connaisseur
Connaisseur is a dedicated Kubernetes admission controller that focuses specifically on image signature verification. It acts as a gatekeeper that ensures only images signed by trusted authorities can be deployed to your cluster.
Key Features
- Multi-Tool Support: Can verify signatures from both Sigstore (Cosign) and Notary (v1 and v2).
- Flexible Trust Roots: Allows you to define different trusted signers for different images.
- Policy-as-Code: Policies are defined in YAML and can be version-controlled.
- Detection Mode: Can run in a “non-blocking” mode to audit existing images.
- Easy Installation: Can be deployed quickly via Helm charts.
Pros
- Purpose-built for image verification, leading to a very focused feature set.
- Supports older Notary signatures alongside modern Sigstore ones.
Cons
- Adding another admission controller can increase cluster complexity.
- Development pace is slower than Kyverno or Policy Controller.
Platforms / Deployment
Kubernetes — Cloud / Hybrid
Security & Compliance
Offers a specialized solution for strict image provenance enforcement.
Integrations & Ecosystem
Works well with various registries and signing tools.
Support & Community
A smaller but dedicated community of security professionals.
8. Tekton Chains
Tekton Chains is an extension for the Tekton CI/CD platform that automatically handles the signing of build artifacts. It observes the build process and generates signatures and provenance attestations without requiring manual steps from the developer.
Key Features
- Automated Signing: Signs artifacts as soon as a build task is completed.
- Provenance Generation: Automatically creates SLSA-compliant build metadata.
- Storage Flexibility: Can store signatures in OCI registries, GCS buckets, or local files.
- Sigstore Native: Built to work with Cosign, Fulcio, and Rekor by default.
- Non-Intrusive: Works in the background without modifying existing build scripts.
Pros
- Ideal for teams already using Tekton for their CI/CD pipelines.
- Drastically simplifies the process of achieving high SLSA levels.
Cons
- Only works within the Tekton ecosystem.
- Can be complex to set up for teams new to Tekton.
Platforms / Deployment
Kubernetes (Tekton) — Cloud / Hybrid
Security & Compliance
Significantly improves the security of the build pipeline itself.
Integrations & Ecosystem
Deeply integrated with Tekton Pipelines and the Sigstore project.
Support & Community
Supported by the Tekton community and OpenSSF.
9. Ratify
Ratify is an open-source verification engine that allows Kubernetes clusters to verify images and other OCI artifacts before deployment. It is designed to be highly extensible and works alongside Gatekeeper to enforce security policies.
Key Features
- Extensible Verifiers: Can verify signatures, SBOMs, and vulnerability reports.
- Referrers API Support: Uses the latest OCI standards to find related metadata for an image.
- Multi-Registry Integration: Works seamlessly across different cloud provider registries.
- High-Performance Verification: Designed for low latency in large-scale clusters.
- Gatekeeper Integration: Often used as an external data source for OPA Gatekeeper.
Pros
- Very flexible and can verify more than just simple signatures.
- Future-proofed by supporting the newest OCI “Referrers” specifications.
Cons
- Requires OPA Gatekeeper for active enforcement.
- The configuration can be more complex than Kyverno.
Platforms / Deployment
Kubernetes — Cloud / Hybrid
Security & Compliance
Excellent for complex environments with multiple types of security metadata.
Integrations & Ecosystem
Strong ties to the Notary Project and Microsoft’s security stack.
Support & Community
An active project within the deislabs community and supported by major cloud vendors.
10. Gitsign
Gitsign is a Sigstore tool specifically for signing Git commits. While most other tools on this list focus on the final container image, Gitsign secures the very beginning of the supply chain by ensuring that every line of code is signed by a verified identity.
Key Features
- Keyless Commit Signing: Uses OIDC (GitHub/Google) to sign Git commits instead of GPG keys.
- No GPG Required: Eliminates the headache of managing local GPG keyrings.
- Transparency Logging: Records every signed commit in the Rekor log for public audit.
- Identity-Based Trust: Commits are tied to a real person’s email or identity.
- Standard Git Integration: Works as a drop-in replacement for standard Git signing.
Pros
- Makes Git signing accessible to every developer without technical friction.
- Ties code changes directly to verified enterprise identities.
Cons
- Still relatively new; not all Git hosting platforms fully visualize these signatures yet.
- Focused only on the source code level, not the final artifact.
Platforms / Deployment
Windows / macOS / Linux — Self-hosted
Security & Compliance
Critical for preventing “insider threat” or repository hijacking at the source level.
Integrations & Ecosystem
Works with any standard Git client and integrates with the Rekor transparency log.
Support & Community
Part of the core Sigstore project.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. Cosign | Registry Signing | Win, Mac, Linux | Hybrid | Keyless OIDC Signing | 4.8/5 |
| 2. Rekor | Public Auditing | Linux | Cloud | Transparency Log | 4.6/5 |
| 3. Fulcio | Identity Certs | Linux | Cloud | Short-lived CA | 4.5/5 |
| 4. Kyverno | K8s Policy | Kubernetes | Hybrid | Native YAML Policy | 4.7/5 |
| 5. Notation | Enterprise PKI | Win, Mac, Linux | Cloud | OCI Standard Support | 4.3/5 |
| 6. Policy Controller | Sigstore Enforcement | Kubernetes | Hybrid | Rekor Verification | 4.4/5 |
| 7. Connaisseur | Dedicated Gatekeeper | Kubernetes | Hybrid | Multi-Tool Support | 4.2/5 |
| 8. Tekton Chains | Pipeline Automation | Kubernetes | Hybrid | Automated Provenance | 4.5/5 |
| 9. Ratify | Extensible Verify | Kubernetes | Cloud | Referrers API Support | 4.4/5 |
| 10. Gitsign | Source Integrity | Win, Mac, Linux | Self-hosted | GPG-free Git Signing | 4.6/5 |
Evaluation & Scoring of Artifact/Container Signing & Verification Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Perf (10%) | Support (10%) | Value (15%) | Total |
| 1. Cosign | 10 | 9 | 10 | 9 | 9 | 9 | 9 | 9.3 |
| 2. Rekor | 8 | 6 | 9 | 10 | 8 | 9 | 8 | 8.1 |
| 3. Fulcio | 8 | 5 | 8 | 10 | 9 | 8 | 8 | 7.6 |
| 4. Kyverno | 9 | 9 | 9 | 8 | 8 | 10 | 9 | 8.9 |
| 5. Notation | 8 | 7 | 8 | 8 | 9 | 8 | 7 | 7.8 |
| 6. Policy Controller | 8 | 7 | 9 | 9 | 8 | 8 | 8 | 8.1 |
| 7. Connaisseur | 7 | 8 | 7 | 8 | 8 | 7 | 8 | 7.4 |
| 8. Tekton Chains | 9 | 6 | 8 | 9 | 8 | 8 | 8 | 8.1 |
| 9. Ratify | 8 | 6 | 8 | 8 | 8 | 8 | 7 | 7.5 |
| 10. Gitsign | 8 | 9 | 7 | 9 | 9 | 8 | 9 | 8.3 |
The scoring indicates that Cosign and Kyverno are currently the most balanced tools for production use, offering a high degree of core functionality and excellent support. Tools like Fulcio and Rekor score higher on security but are more complex to manage if you are running your own infrastructure.
Which Artifact/Container Signing Tool Is Right for You?
Solo / Freelancer
If you are an individual developer or a small team, Cosign is the only tool you need to start. Its keyless mode means you can sign your public images using your existing GitHub account without any cost or infrastructure setup.
SMB (Small to Medium Business)
For small to medium businesses, using Cosign in your CI/CD pipelines combined with Kyverno in your Kubernetes clusters provides a comprehensive security loop. This setup is easy to maintain and highly effective at blocking unauthorized images.
Mid-Market
Organizations with growing compliance needs should look into Tekton Chains or GitHub Artifact Attestations (built on Sigstore). These provide automated proof of how software was built, which is vital for passing security audits.
Enterprise
Enterprises with strict PKI requirements or those heavily invested in Azure or AWS may prefer the Notary Project (Notation). It fits better into traditional corporate certificate management workflows while still providing modern OCI security.
Budget vs Premium
The entire Sigstore ecosystem is free and open-source, making it the best “budget” option that still provides “premium” security. The only cost is the time required for engineering teams to implement the workflows.
Feature Depth vs Ease of Use
Cosign is the easiest to use, while Kyverno offers the most feature depth for Kubernetes users who want to verify more than just signatures, such as SBOMs and vulnerability scan results.
Integrations & Scalability
For massive, multi-cluster environments, Policy Controller or Ratify offer the best scalability by integrating deeply with the cluster’s existing security framework and public transparency logs.
Security & Compliance Needs
If you require the highest level of auditability, you must use a tool that integrates with a transparency log like Rekor. This ensures that even if a signing identity is compromised later, you have a verifiable record of exactly when the artifact was signed.
Frequently Asked Questions (FAQs)
1. What is the difference between keyless and key-based signing?
Key-based signing requires you to manage and protect a permanent private key. Keyless signing uses your identity (like email) to get a temporary certificate, eliminating the risk of a stolen key.
2. Is Sigstore only for container images?
No, Sigstore and Cosign can sign almost any software artifact, including binary files, blobs, Git commits, and Helm charts.
3. Do I need to pay to use Rekor or Fulcio?
No, the public instances of Rekor and Fulcio provided by the Sigstore project are free for everyone to use.
4. Can I use these tools in an air-gapped environment?
Yes, but you will need to host your own private instances of the Sigstore infrastructure (Fulcio and Rekor) or use traditional key-based signing.
5. How do I verify a signature during deployment?
You use an admission controller like Kyverno or Sigstore Policy Controller in your Kubernetes cluster to check the signature before the pod is allowed to start.
6. Does signing a container slow down the build process?
The signing process itself takes only a few seconds. Verification during deployment also has a negligible impact on performance.
7. What happens if the Sigstore public services go down?
If you rely on public keyless signing, you may be unable to sign new artifacts. However, existing signatures can still be verified if you have cached the necessary public information.
8. Can one image have multiple signatures?
Yes, modern tools allow multiple different identities or systems to sign a single image, which is useful for “promotion” workflows between dev and prod.
9. Is Docker Content Trust still the standard?
No, Docker is retiring Docker Content Trust in favor of modern standards like Sigstore and the Notary Project.
10. Do these tools help with SLSA compliance?
Yes, tools like Tekton Chains and Cosign are specifically designed to help organizations reach SLSA Level 3 or higher by providing verifiable provenance.
Conclusion
Securing the software supply chain is no longer an optional task for modern DevOps teams. The rise of sophisticated attacks on build systems has made artifact signing and verification a foundational requirement for any production environment. By adopting the Sigstore ecosystem—specifically tools like Cosign, Rekor, and Fulcio—organizations can implement a robust, identity-based security model that eliminates the headaches of traditional key management. Whether you choose the flexibility of Kyverno or the enterprise focus of Notation, the goal remains the same: ensuring that what you run is exactly what you built. As the industry continues to move toward Zero Trust, the tools and standards in this space will only become more integrated and automated. The key is to start small—begin by signing your images in CI/CD and gradually move toward enforcing those signatures at the cluster level. This incremental approach allows your team to build the necessary expertise while significantly reducing your organization’s risk profile.
Best Cardiac Hospitals Near You
Discover top heart hospitals, cardiology centers & cardiac care services by city.
Advanced Heart Care • Trusted Hospitals • Expert Teams
View Best Hospitals