Top 10 Payment Fraud Scoring APIs: Features, Pros, Cons & Comparison
Introduction Payment fraud scoring APIs have become the primary defense line for the modern digital economy. In an era where transactions happen in milliseconds, manual review is…
Top 10 Digital Wallet SDKs: Features, Pros, Cons & Comparison
Introduction Digital Wallet Software Development Kits (SDKs) have become the essential building blocks for modern commerce, enabling businesses to integrate secure payment and asset management features directly…
Top 10 BNPL Platforms: Features, Pros, Cons & Comparison
Introduction Buy Now, Pay Later (BNPL) has transformed from a niche e-commerce feature into a fundamental pillar of global consumer finance. By providing a bridge between immediate…
Top 10 API Aggregators: Features, Pros, Cons & Comparison
Introduction In the modern software ecosystem, the proliferation of specialized SaaS applications has created a fragmented landscape. Developers often find themselves writing and maintaining dozens of unique…
Top 10 Open Banking Platforms: Features, Pros, Cons & Comparison
Introduction Open banking has transitioned from a regulatory requirement into a fundamental piece of financial infrastructure. In plain English, an open banking platform is a secure gateway…
Top 10 Tax Tools for Crypto: Features, Pros, Cons & Comparison
Introduction Cryptocurrency tax compliance has moved from a niche concern for early adopters to a primary focus for global regulatory bodies. As tax authorities implement sophisticated tracking…
Top 10 Digital Asset Compliance Tools: Features, Pros, Cons & Comparison
Introduction Digital asset compliance has shifted from a niche requirement for specialized startups into a foundational pillar for the global financial ecosystem. As cryptocurrencies, stablecoins, and tokenized…
Top 10 Crypto Custody Platforms: Features, Pros, Cons & Comparison
Introduction Crypto custody has transitioned from a niche technical requirement for early adopters into a foundational pillar of the global financial ecosystem. As institutional capital continues to…
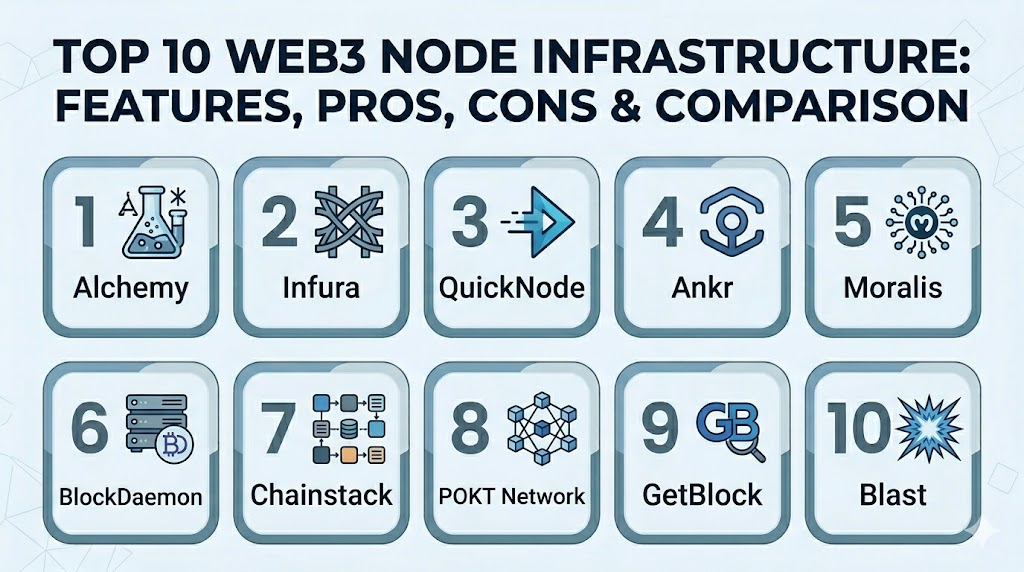
Top 10 Web3 Node Infrastructure: Features, Pros, Cons & Comparison
Introduction Web3 node infrastructure is the underlying hardware and software layer that allows developers to interact with blockchain networks. Without a node, a decentralized application (dApp) has…