Best Cosmetic Hospitals Near You
Compare top cosmetic hospitals, aesthetic clinics & beauty treatments by city.
Trusted • Verified • Best-in-Class Care
Explore Best HospitalsTop 10 IT Financial Management Tools: Features, Pros, Cons & Comparison
Introduction IT Financial Management (ITFM) has transitioned from a back-office accounting function into a strategic pillar of modern technology operations. As digital transformation accelerates, the ability to…
Top 10 Asset Lifecycle Management Tools: Features, Pros, Cons & Comparison
Introduction Asset Lifecycle Management (ALM) is the strategic process of optimizing the profit generated by an asset throughout its entire lifespan—from initial planning and acquisition to operation,…
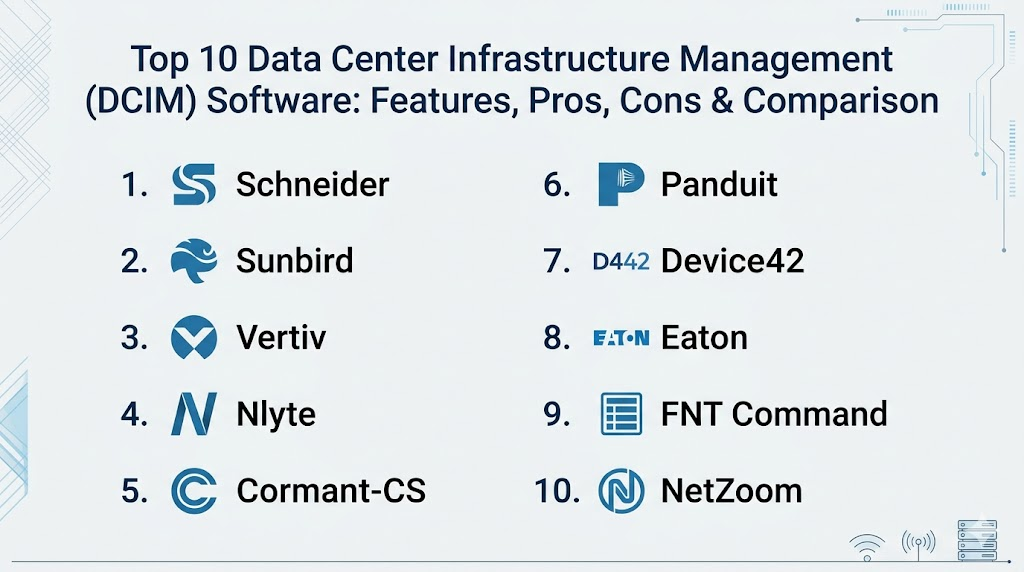
Top 10 Data Center Infrastructure Management (DCIM) Software: Features, Pros, Cons & Comparison
Introduction Data Center Infrastructure Management (DCIM) software has become the central nervous system of the modern facility, bridging the historical gap between traditional IT operations and physical…
Top 10 Web Content Filtering Tools: Features, Pros, Cons & Comparison
Introduction Web content filtering has transitioned from a basic “block-list” utility into a critical component of the modern cybersecurity fabric. In an era where the web is…
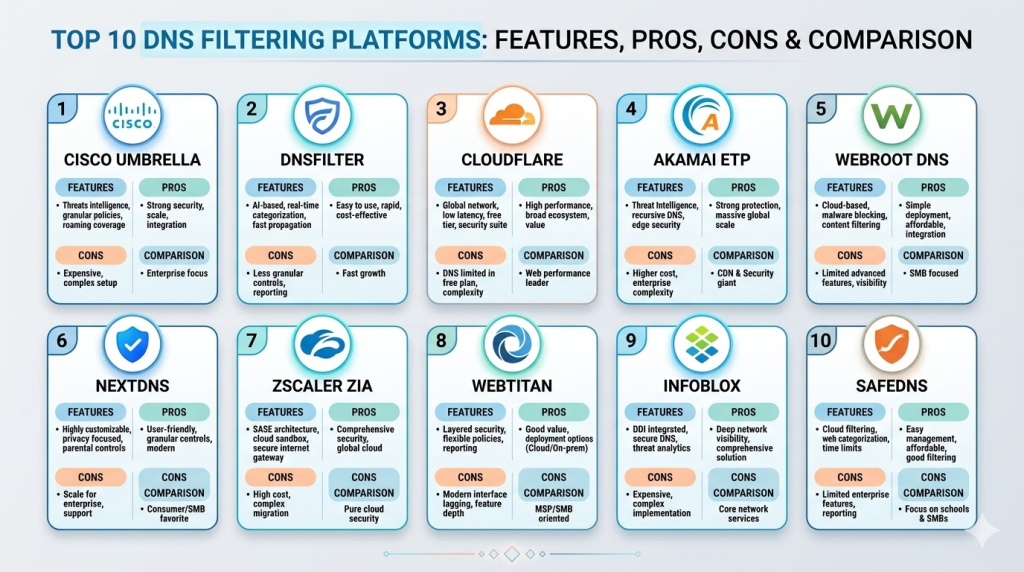
Top 10 DNS Filtering Platforms: Features, Pros, Cons & Comparison
Introduction DNS filtering has become one of the most effective and easiest-to-deploy layers of a modern “defense-in-depth” security strategy. By intercepting web requests at the Domain Name…
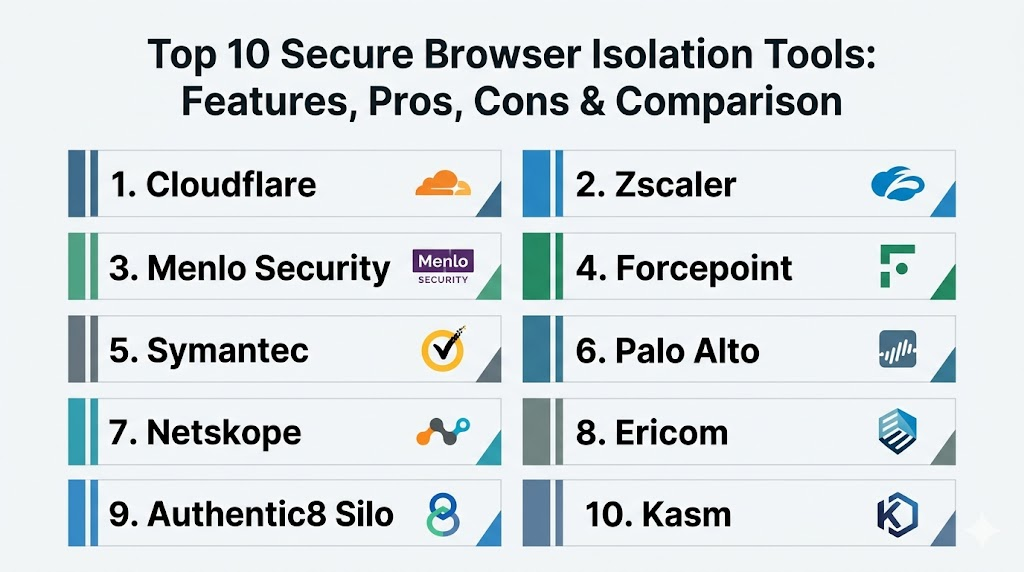
Top 10 Secure Browser Isolation Tools: Features, Pros, Cons & Comparison
Introduction Secure Browser Isolation (SBI), often referred to as Remote Browser Isolation (RBI), is a cybersecurity technology that physically separates a user’s browsing activity from their local…
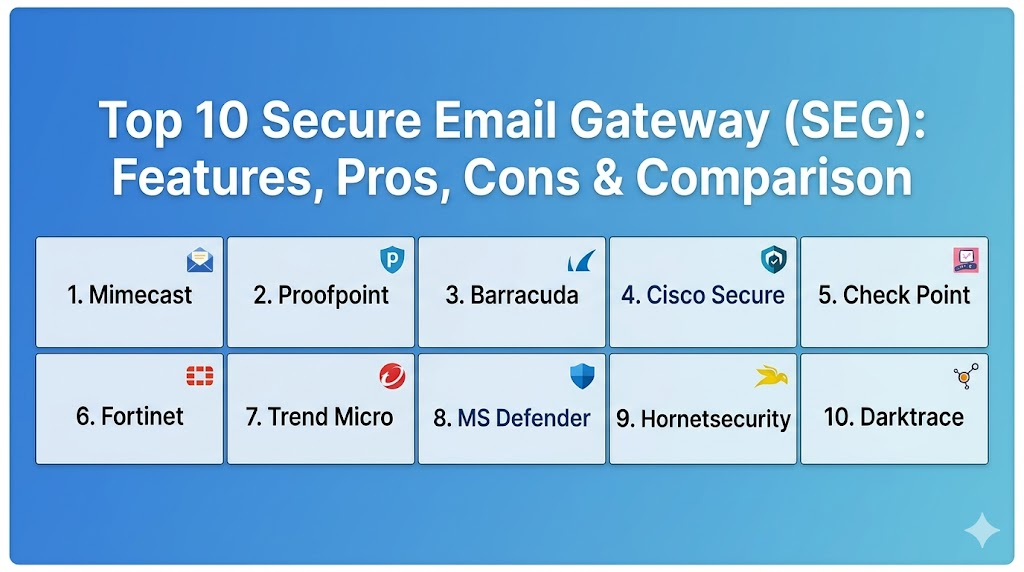
Top 10 Secure Email Gateway (SEG): Features, Pros, Cons & Comparison
Introduction Email remains the primary vector for cyberattacks, with phishing, ransomware, and business email compromise (BEC) accounting for the vast majority of successful breaches. A Secure Email…
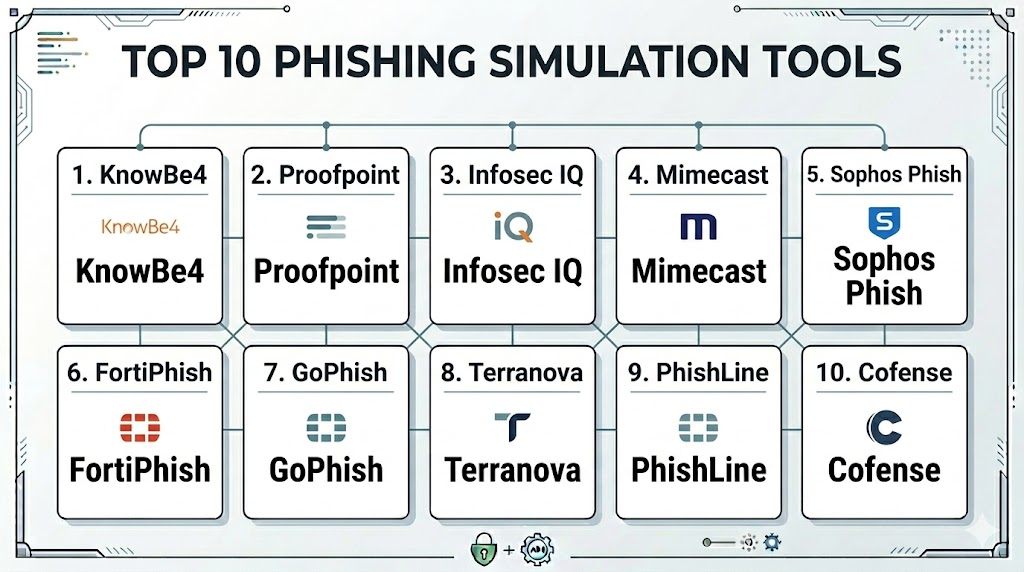
Top 10 Phishing Simulation Tools: Features, Pros, Cons & Comparison
Introduction Phishing simulation tools have become an indispensable component of the modern cybersecurity framework, moving beyond simple “click-testing” to become comprehensive human risk management platforms. As technical…
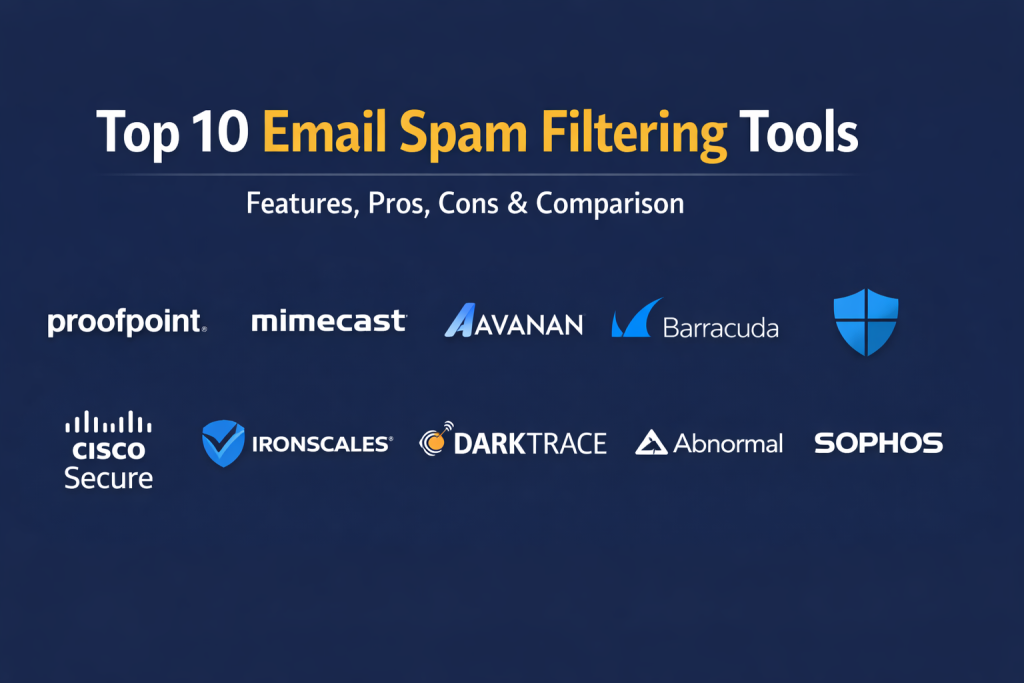
Top 10 Email Spam Filtering Tools: Features, Pros, Cons & Comparison
Introduction Email remains the primary communication vector for global business, making it the most targeted entry point for cyber threats. Modern spam filtering has evolved far beyond…
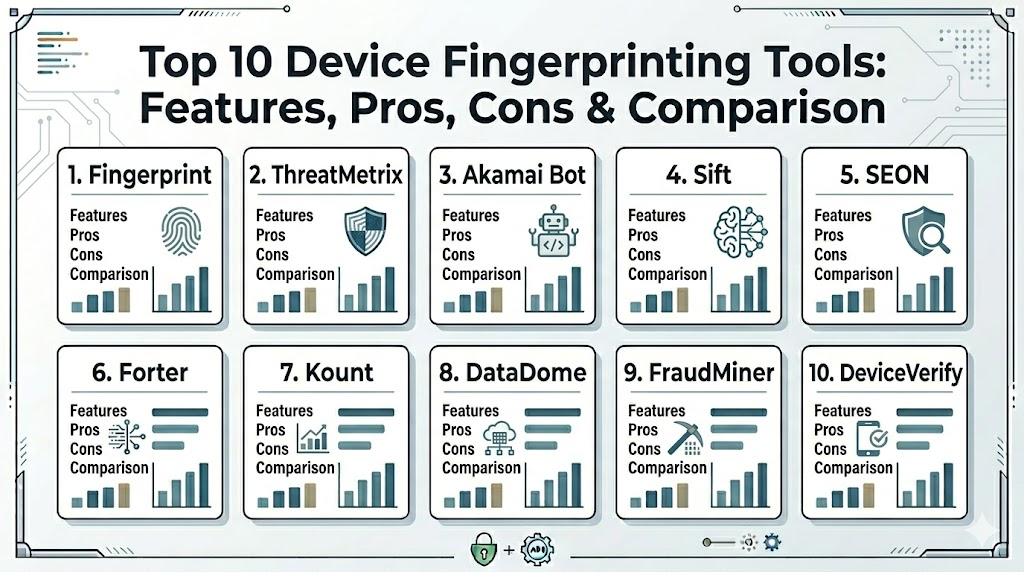
Top 10 Device Fingerprinting Tools: Features, Pros, Cons & Comparison
Introduction Device fingerprinting has become a critical layer in the modern cybersecurity and fraud prevention stack. Unlike traditional tracking methods like cookies, which are easily cleared or…