Best Cosmetic Hospitals Near You
Compare top cosmetic hospitals, aesthetic clinics & beauty treatments by city.
Trusted • Verified • Best-in-Class Care
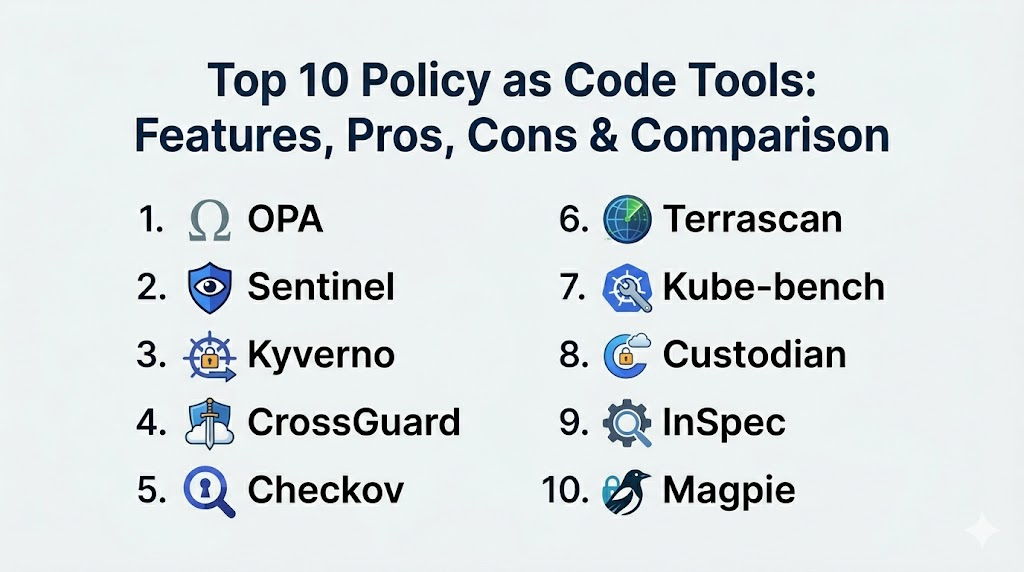
Explore Best HospitalsTop 10 Policy as Code Tools: Features, Pros, Cons & Comparison
Introduction Policy as Code (PaC) has shifted from a niche security requirement to a fundamental pillar of modern infrastructure management. In the age of rapid cloud deployments…
Top 10 Adversarial Robustness Testing Tools: Features, Pros, Cons & Comparison
Introduction Adversarial robustness testing is the specialized process of evaluating how machine learning models behave when subjected to malicious, intentionally crafted inputs known as adversarial attacks. These…
Top 10 Artifact/Container Signing & Verification Tools (Sigstore)
Introduction Artifact and container signing is a critical security practice used to verify the origin and integrity of software components. In a modern software supply chain, a…
Top 10 Secure Software Supply Chain Attestation Tools (SLSA/Provenance)
Introduction Secure software supply chain attestation tools are specialized security solutions designed to verify the integrity and origin of software throughout its development lifecycle. In an era…
Top 10 Container Security Tools: Features, Pros, Cons and Comparison
Introduction Container Security Tools help teams secure container images, registries, Kubernetes clusters, and container runtime behavior. In simple terms, they prevent insecure images from being built and…
Top 10 Cloud Workload Protection Platforms: Features, Pros, Cons and Comparison
Introduction Cloud Workload Protection Platforms help security teams protect workloads running in the cloud and modern environments such as virtual machines, containers, Kubernetes clusters, and sometimes serverless…
Top 10 Cloud Security Posture Management Tools: Features, Pros, Cons and Comparison
Introduction Cloud Security Posture Management tools help you continuously find and fix risky cloud settings across accounts, subscriptions, projects, and services. In simple terms, CSPM tools scan…
Top 10 Code Signing Tools: Features, Pros, Cons and Comparison
Introduction Code signing tools help teams prove that software releases are authentic and have not been tampered with after build time. They attach a digital signature to…
Top 10 Certificate Management Tools: Features, Pros, Cons and Comparison
Introduction Certificate management tools help teams issue, store, renew, rotate, and monitor digital certificates used for TLS encryption, service identity, mutual TLS, and secure internal and external…
Top 10 Secrets Management Tools: Features, Pros, Cons and Comparison
Introduction Secrets management tools store, protect, rotate, and control access to sensitive values like API keys, database passwords, certificates, tokens, and encryption keys. Instead of hardcoding secrets…