1. Introduction to Quantum Computing
Quantum Computing is a cutting-edge technology that leverages the principles of quantum mechanics to perform calculations at speeds unimaginable with classical computers.
Key Concepts in Quantum Computing:
- Superposition
- Entanglement
- Quantum Gates
Applications of Quantum Computing:
- Quantum Cryptography
- Quantum Simulation
- Optimization Problems
Understanding the basics of quantum computing is essential for exploring its vast potential in revolutionizing various industries.
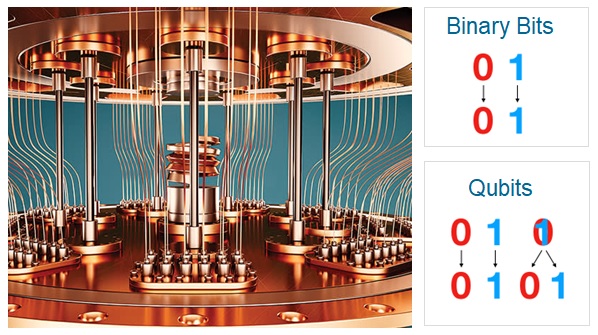
2. Principles of Quantum Mechanics in Quantum Computing
In quantum computing, the principles of quantum mechanics play a crucial role in the design and operation of quantum computers.
Key Concepts:
- Superposition: Allows quantum systems to exist in multiple states simultaneously.
- Entanglement: The phenomenon where quantum particles become correlated and their states are interdependent.
- Quantum Gates: Analogous to classical logic gates but operate on quantum bits (qubits).
These principles form the basis of quantum computing algorithms and enable the processing of complex computations at speeds far exceeding classical computers.
:max_bytes(150000):strip_icc()/quantum-computing.asp-FINAL-1-68635090f7534414b9173598fe0ad95c.png)
Quantum Computing
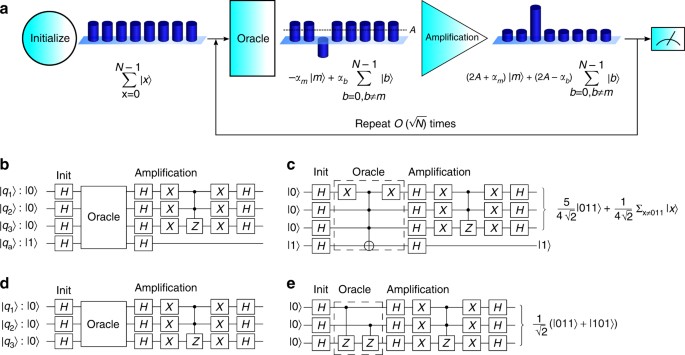
3. Quantum Computing Algorithms
Quantum computing algorithms are designed to leverage the unusual properties of quantum mechanics to perform calculations that would be impossible or impractical with classical computers.
Key features of quantum computing algorithms include:
- Superposition
- Entanglement
- Interference
Examples of quantum computing algorithms:
- Shor’s algorithm
- Grover’s algorithm
- Quantum phase estimation algorithm
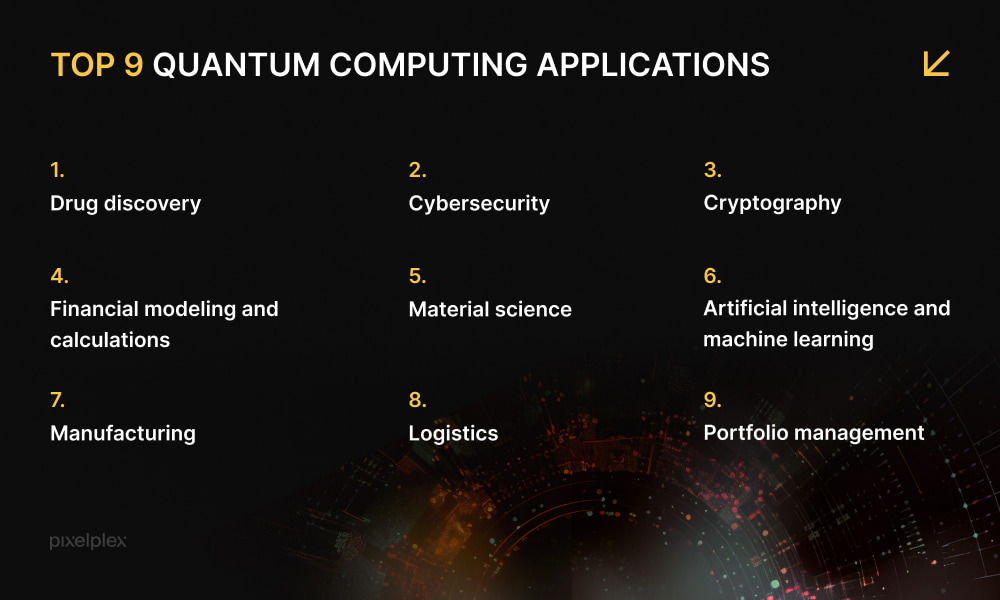
4. Applications of Quantum Computing
Quantum computing has a wide range of potential applications across various fields. Some of the key areas where quantum computing is expected to make a significant impact include:
1. Quantum Cryptography
Quantum cryptography leverages the principles of quantum mechanics to create secure communication channels that are theoretically immune to eavesdropping.
2. Optimization Problems
- Solving complex optimization problems more efficiently than classical algorithms.
- Applications in logistics, financial modeling, drug discovery, etc.
3. Machine Learning
- Enhancing machine learning algorithms for improved pattern recognition and data analysis.
- Potential for faster training of deep learning networks.
5. Challenges and Future of Quantum Computing
Quantum computing presents several challenges that need to be addressed for its advancement:
- Noise and errors: Quantum systems are susceptible to errors and noise, requiring robust error correction techniques.
- Scalability: Scaling quantum systems to a large number of qubits while maintaining coherence is a major challenge.
- Interfacing with classical computers: Integrating quantum and classical computing systems efficiently is crucial for practical applications.
- Algorithm development: Developing quantum algorithms that outperform classical algorithms for specific tasks remains a key research area.
The future of quantum computing holds promise for revolutionizing various fields such as cryptography, optimization, and material science. Overcoming current challenges will pave the way for harnessing the full potential of quantum computing.
Best Cardiac Hospitals Near You
Discover top heart hospitals, cardiology centers & cardiac care services by city.
Advanced Heart Care • Trusted Hospitals • Expert Teams
View Best Hospitals